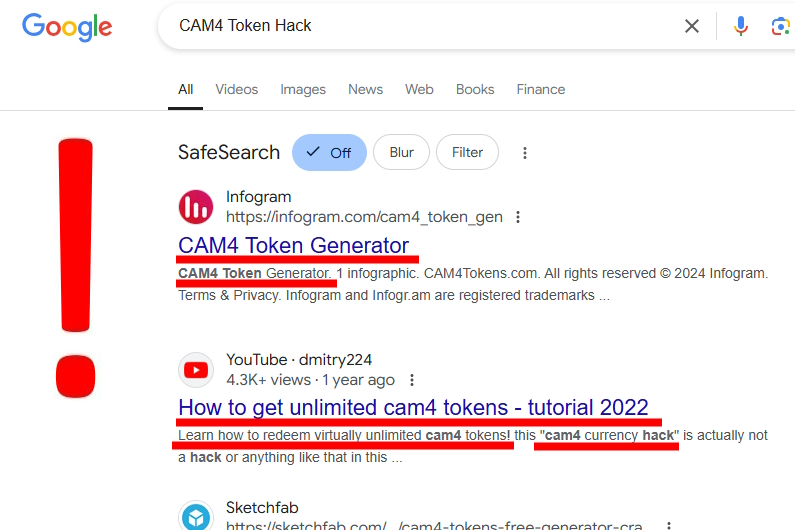
Nowadays, streaming platforms are extremely popular, attracting millions of users from all over the world. Their availability and the variety of content they offer make them one of the main sources of entertainment on the Internet. Unfortunately, with their growing popularity, various types of scams also appear. More and more often, you can come across fake sites offering the so-called CAM4 Token Generator or CAM4 hack, which supposedly provides free access to paid content. Criminals take advantage of users’ natural desire to save money by creating convincing but dangerous traps.
This article aims to warn against such dangerous practices and explain why you should be especially careful. The problem of fake token generators and CAM4 cheat programs is becoming more and more serious, leading to significant financial losses and theft of personal data. Scammers are becoming more and more sophisticated in their methods, using advanced social engineering techniques and creating sites that are confusingly similar to the original services. Users must be aware of these threats and know how to protect themselves from attacks.
And if you are interested in a general description of the site – we invite you to read CAM4 Review. This site is not only about generator threats, but also a lot of great fun!
How to hack CAM4?
It should be clear – there is no safe and legal way to bypass the payment systems on streaming platforms. This is a fact that is often met with disbelief by users, especially when they see convincing ads or recommendations for CAM4 Token Generator or CAM4 hack. Any sites offering CAM4 cheat or CAM4 token cheat are, in fact, prepared by cyber criminals. Streaming platforms invest significant resources in securing their payment systems, using advanced encryption technologies and multi-level security systems that cannot be simply hacked with a simple program found on the Internet.
The only goal of scammers is to extort sensitive data or money from unwary users. Criminals often create elaborate stories and “evidence” of their tools’ operation using fabricated screenshots, fake reviews, or even fake social media accounts. They can also use bots to generate positive comments and ratings, creating the illusion of credibility of their illegal services. Situations where scammers demand a “small verification fee” or ask for credit card details “to confirm your age” are particularly dangerous – these are classic fraud techniques that can lead to severe financial losses.
Typical online fraud mechanisms
Scammers use a variety of methods to lure potential victims. Here are the most popular techniques:
- Fake token generators.
- Websites pretending to be official services.
- Programs promising free access.
- Fake contests and promotions.
- Counterfeit mobile applications.
Sites that impersonate well-known services, using similar domain names and layouts, are particularly dangerous. Scammers often create convincing copies of real platforms to gain users’ trust.
Consequences of Using Fake Sites
Attempts to use illegal tools like CAM4 Generator can lead to serious consequences. Users who fall for such scams often experience the following:
- Personal data theft – Criminals can use stolen information to create false documents and take out loans in their name. In many cases, stolen data is sold on the black market to other criminal groups who use it for various illegal activities. The process of recovering a stolen identity can take months, sometimes even years, causing severe problems in everyday life, from the inability to open a bank account to difficulties in finding a job.
- Losing money from bank accounts – Fraudsters who gain access to login details can empty their bank accounts in minutes through a series of quick transactions. Transfers are often directed to accounts in different countries, making tracking and recovering the funds much more difficult. Additionally, criminals can use our details to take out payday loans or make a series of small card payments that may initially escape our attention.
- Malware infections – Malware can run in the background for a long, collecting our data and browsing habits. Some types of malware can take control of the camera and microphone, which poses a serious privacy risk. Additional programs like ransomware are often installed that encrypt our files and demand a ransom to unlock them.
- Social media account hacks – Criminals often impersonate us after taking over our social media accounts, trying to extort money from friends, or spreading malicious links. Losing access to accounts can also mean losing valuable memories, photos, and contacts collected over the years. In the case of business accounts, hacking can lead to serious image and financial losses.
- Blackmail and extortion – Cybercriminals may threaten to reveal private information or compromising material, even if none exists. They often use an intimidation technique, claiming that they have access to the victim’s webcam and have recorded compromising material. Blackmailers usually demand payment in cryptocurrencies, which makes them difficult to track, and fulfilling their demands often only leads to further extortion attempts.
Personal data theft
Fraudsters use stolen personal data in many ways. They can sell it on the black market, create fake accounts, take out loans, or commit other financial crimes. Sharing scans of documents or credit card details is particularly dangerous.
How to protect yourself against fraud?
To protect yourself from scams involving fake token generators and hacks, you should follow some basic safety rules:
- Only use official websites and applications.
- Never provide personal information on suspicious sites.
- Do not install unknown programs promising free access.
- Use strong, unique passwords.
- Enable two-step authentication where possible.
- Regularly update systems and antivirus programs.
Rules for safe use of the internet
The basic principles of cybersecurity include:
- Regularly updating operating systems and browsers.
- Using up-to-date antivirus software.
- Avoiding clicking on suspicious links and attachments.
- Checking URLs before logging in.
- Not sharing login details.
- Regularly monitoring activity on bank accounts.

Summary of CAM4 Token Hack
In summary, any promises of free access through CAM4 token hack or similar tools are scams. There are no legal methods for bypassing payment systems on streaming platforms. Attempts to use such solutions inevitably lead to problems, often with serious financial and legal consequences.
Remember that online security depends primarily on users’ conscious decisions. If an offer seems too good to be true, it is most likely a scam. Be especially careful with suspicious offers, and always follow the principle of limited trust when using the Internet.